This is the 19th article in the award-winning “Real Words or Buzzwords?” series about how real words become empty words and stifle technology progress, also published on SecurityInfoWatch.com.
By Ray Bernard, PSP, CHS-III
We need the term “serverless” in order to get our wits around the current state of cloud computing, which offers application execution capabilities that are a very close match for the nature of security monitoring and response—whether logical or physical. It is what security industry products need to keep up with the world they are intended to monitor and protect.
All-in-one RWOB
MAXIMIZE YOUR SECURITY OPERATIONS CAPABILITIES
Upgrade your security operations effectiveness through Security Technology Strategic Planning. Provably get more for your company's security technology investment.
★ ★ ★ GET NOTIFIED! ★ ★ ★
SIGN UP to be notified by email the day a new Real Words or Buzzwords? article is posted!
Real Words or Buzzwords?
The Award-Winning Article Series
#1 Proof of the buzzword that killed tech advances in the security industry—but not other industries.
#2 Next Generation (NextGen): A sure way to tell hype from reality.
#3 Customer Centric: Why all security industry companies aren't customer centric.
#4 Best of Breed: What it should mean to companies and their customers.
#5 Open: An openness scale to rate platforms and systems
#6 Network-friendly: It's much more than network connectivity.
#7 Mobile first: Not what it sounds like.
#8 Enterprise Class (Part One): To qualify as Enterprise Class system today is world's beyond what it was yesterday.
#9 Enterprise Class (Part Two): Enterprise Class must be more than just a top-level label.
#10 Enterprise Class (Part Three): Enterprise Class must be 21st century technology.
#11 Intuitive: It’s about time that we had a real-world testable definition for “intuitive”.
#12 State of the Art: A perspective for right-setting our own thinking about technologies.
#13 True Cloud (Part One): Fully evaluating cloud product offerings.
#14 True Cloud (Part Two): Examining the characteristics of 'native-cloud' applications.
#15 True Cloud (Part Three): Due diligence in testing cloud systems.
#16 IP-based, IP-enabled, IP-capable, or IP-connectable?: A perspective for right-setting our own thinking about technologies.
#17 Five Nines: Many people equate high availability with good user experience, yet many more factors are critically important.
#18 Robust: Words like “robust” must be followed by design specifics to be meaningful.
#19 Serverless Computing – Part 1: Why "serverless computing" is critical for some cloud offerings.
#20 Serverless Computing – Part 2: Why full virtualization is the future of cloud computing.
#21 Situational Awareness – Part 1: What products provide situational awareness?
#22 Situational Awareness – Part 2: Why system designs are incomplete without situational awareness?
#23 Situational Awareness – Part 3: How mobile devices change the situational awareness landscape?
#24 Situational Awareness – Part 4: Why situational awareness is a must for security system maintenance and acceptable uptime.
#25 Situational Awareness – Part 5: We are now entering the era of smart buildings and facilities. We must design integrated security systems that are much smarter than those we have designed in the past.
#26 Situational Awareness – Part 6: Developing modern day situational awareness solutions requires moving beyond 20th century thinking.
#27 Situational Awareness – Part 7: Modern day incident response deserves the help that modern technology can provide but doesn’t yet. Filling this void is one of the great security industry opportunities of our time.
#28 Unicity: Security solutions providers can spur innovation by envisioning how the Unicity concept can extend and strengthen physical access into real-time presence management.
#29 The API Economy: Why The API Economy will have a significant impact on the physical security industry moving forward.
#31 The Built Environment: In the 21st century, “the built environment” means so much more than it did just two decades ago.
#32 Hyper-Converged Infrastructure: Hyper-Converged Infrastructure has been a hot phrase in IT for several years, but do its promises hold true for the physical security industry?
#33 Software-Defined: Cloud-computing technology, with its many software-defined elements, is bringing self-scaling real-time performance capabilities to physical security system technology.
#34 High-Performance: How the right use of "high-performance" can accelerate the adoption of truly high-performing emerging technologies.
#35 Erasure Coding: Why RAID drive arrays don’t work anymore for video storage, and why Erasure Coding does.
#36 Presence Control: Anyone responsible for access control management or smart building experience must understand and apply presence control.
#37 Internet+: The Internet has evolved into much more than the information superhighway it was originally conceived to be.
#38 Digital Twin: Though few in physical security are familiar with the concept, it holds enormous potential for the industry.
#39 Fog Computing: Though commonly misunderstood, the concept of fog computing has become critically important to physical security systems.
#40 Scale - Part 1: Although many security-industry thought leaders have advocated that we should be “learning from IT,” there is still insufficient emphasis on learning about IT practices, especially for large-scale deployments.
#41 Scale - Part 2: Why the industry has yet to fully grasp what the ‘Internet of Things’ means for scaling physical security devices and systems.
#42 Cyberspace - Part 1: Thought to be an outdated term by some, understanding ‘Cyberspace’ and how it differs from ‘Cyber’ is paramount for security practitioners.
#43 Cyber-Physical Systems - Part 1: We must understand what it means that electronic physical security systems are cyber-physical systems.
#44 Cyberspace - Part 2: Thought to be an outdated term by some, understanding ‘Cyberspace’ and how it differs from ‘Cyber’ is paramount for security practitioners.
#45 Artificial Intelligence, Machine Learning and Deep Learning: Examining the differences in these technologies and their respective benefits for the security industry.
#46 VDI – Virtual Desktop Infrastructure: At first glance, VDI doesn’t seem to have much application to a SOC deployment. But a closer look reveals why it is actually of critical importance.
#47 Hybrid Cloud: The definition of hybrid cloud has evolved, and it’s important to understand the implications for physical security system deployments.
#48 Legacy: How you define ‘legacy technology’ may determine whether you get to update or replace critical systems.
#49 H.264 - Part 1: Examining the terms involved in camera stream configuration settings and why they are important.
#50 H.264 - Part 2: A look at the different H.264 video frame types and how they relate to intended uses of video.
#51 H.264 - Part 3: Once seen as just a marketing term, ‘smart codecs’ have revolutionized video compression.
#52 Presence Technologies: The proliferation of IoT sensors and devices, plus the current impacts of the COVID-19 pandemic, have elevated the capabilities and the importance of presence technologies.
#53 Anonymization, Encryption and Governance: The exponential advance of information technologies requires an exponential advance in the application of data protection.
#54 Computer Vision: Why a good understanding of the computer vision concept is important for evaluating today’s security video analytics products.
#55 Exponential Technology Advancement: The next 10 years of security technology will bring more change than in the entire history of the industry to now.
#56 IoT and IoT Native: The next 10 years of security technology will bring more change than in the entire history of the industry to now.
#57 Cloud Native IoT: A continuing look at what it means to have a 'True Cloud' solution and its impact on today’s physical security technologies.
#58 Bluetooth vs. Bluetooth LE: The next 10 years of security technology will bring more change than in the entire history of the industry to now.
#59 LPWAN - Low-Power Wide Area Networks: Emerging IoT smart sensor devices and systems are finding high-ROI uses for building security and safety.
#60 Edge Computing and the Evolving Internet: Almost 15 billion personal mobile devices and over 22 billion IoT devices operating daily worldwide have shifted the Internet’s “center of gravity” from its core to its edge – with many implications for enterprise physical security deployments
#61 Attack Surface: (Published as a Convergence Q&A Column article)An attack surface is defined as the total number of all possible entry points for unauthorized access into any system.
#62 Autonomous Compute Infrastructure: We’re on the brink of a radical new approach to technology, driven by autonomous operations.
#63 Physical Security Watershed Moment: We have reached a juncture in physical security technology that is making most of our past thinking irrelevant.
#64 Access Chaos: For 50 years we have had to live with physical access control systems that were not manageable at any large scale.
#65 AI and Automatiom: Will engineering talent, business savvy and capital investment from outside the physical security industry bring technology startups that transform reactive security to proactive and preventive security operations?
#66 Interoperability: Over the next five years, the single greatest determinant of the extent to which existing security industry companies will thrive or die is interoperability.
#67 AI Model : One key factor affects the accuracy, speed and computational requirements of AI
#68 Interoperability – Part 2: There are two types of security system interoperability – both of which are important considerations in the design of security systems and the selection of security system products.
#69 Interoperability – Part 3: There are two types of security system interoperability – both of which are important considerations in the design of security systems and the selection of security system products.
#70 Operationalizing AI: AI is not a product, but a broad category of software that enables products and systems to do more than ever before possible. How do we put it to good use?
#71 Shallow IT Adoption – Part 1: It’s not just about being IT compliant, it’s also about leveraging IT capabilities to properly serve the needs and wants of today’s technologically savvy customers.
#72 E-waste – an important security system design issue: Now e-waste is an important design issue not just because of growing e-waste regulations, but because educated designers can save enterprise security system customers a lot of money.
#73 LRPoE - Long Reach Power over Ethernet: A dozen factors have improved the business attractiveness of network cameras, making it more desirable to place cameras further from existing IT closets than the 328 foot limitation of standard Ethernet cable.
#74 NIST Declares Physical Access Control Systems are OT: Does it really mean anything that OT has joined the parade of labels (IT, IoT, and then IIoT) variously getting applied to security systems?
#75 Future Ready: Google sees the term "future-ready" trending up across many subject domains. But does that term apply to the physical security industry and its customers?
#76 Data KLiteracy: AI needs data. Thus, the ability of any department or division in an organization (including security) to use AI effectively depends on its ability to effectively obtain and utilize data – including security.
#77 Security Intelligence (upcoming): AI brings two kinds of intelligence to physical security systems – people bring the third.
More to come about every other week.
“Cloud computing is an internet based technology model that allows users to instantly access, manage and deploy large shared, virtual computing resources.”
For most of us who have worked hands-on with server and workstation deployments for decades, it’s hard to envision computing without servers. After all, the simplest definition of computing is “the use or operation of computers.” Thus, of course, serverless computing does involve computing hardware. This is why, in recent months, I’ve had many people from the security industry decry the term “serverless computing” when I have broached the subject. “That’s a stupid thing to say.” “It’s just a IT marketing trick; there is really no such thing as serverless computing.” One person cleverly remarked, “Whoever thought that term up had their head in the clouds!” That’s exactly right—literally speaking—and it’s where we need to be on this subject.
Why Serverless?
We need the term “serverless” in order to get our wits around the current state of cloud computing, which offers application execution capabilities that are a very closely match for the nature of security monitoring and response—whether logical or physical. It is what security industry products need to keep up with the world they are intended to monitor and protect.
Dalal explains, “Serverless Computing is uniquely suited to event-driven functions. For example, a remote device which monitors a patient’s heart rate can be triggered in the case of an event to provide emergency notification response to hospital systems.” The same thing applies to monitored activity and alarm response.
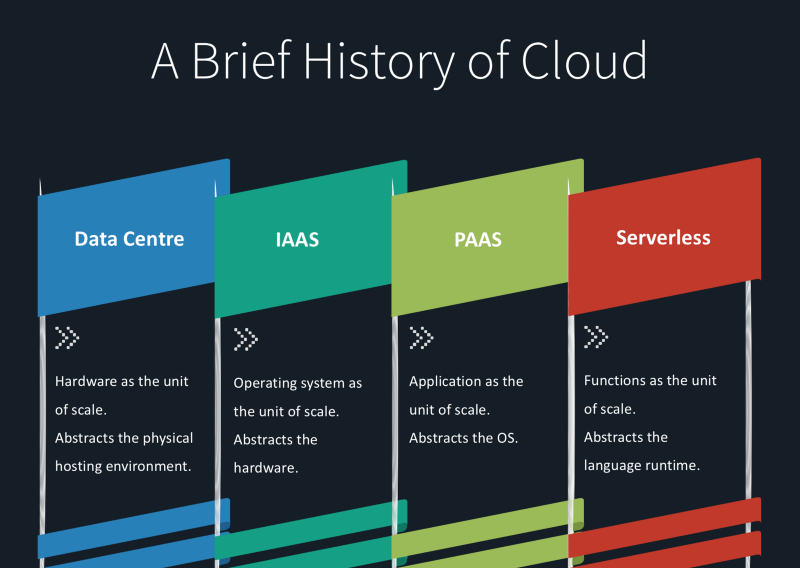
The reason we need the term “serverless” is that we must radically change our thinking about software design and development in order to take advantage of the current state of cloud computing—which has evolved from Infrastructure as a Service (IAAS) to Platform as a Service (PAAS) and now to Functions as a Service (FAAS) – which is serverless computing.
The diagram below provided by AuroSys puts it all in perspective.
In a traditional data center, an entire application (or several) would always be held in memory and “running”, mostly with small parts of the application being used at any one time. Gigaflops of CPU chips, gigabytes of memory and terabytes of disk storage would be energized all the time, even though only small parts of those resources would be utilized. Cloud computing introduced “resource pools”, using virtualization of server hardware. That was easier to picture because it was simply software imitating the server architecture we had always known.
Significant Mind-Shifts
Serverless computing requires two significant mind-shifts, first to the use of “cloud containers”, and then to the step beyond that, which is serverless computing. For decades we have been performing software development in the server context, whether on server hardware or in a virtual machine server. In a cloud data center, that looked like this:
Multiple Applications on
Multiple Operating Systems on
Multiple Virtual Servers on
Server Hardware
Under that server-based architecture, cloud application providers must still manage the virtual server or virtual server cluster on which their applications are running. Then in 2014 along came “application containers”, called containerization, which provided another layer of virtualization. An application container holds only those software code libraries required to run the application being placed in it, as opposed to holding an entire operating system. That stacks up as shown below and in this diagram.
Multiple Applications in
Multiple Application Containers on a
Single Container Engine on a
Single Operating System on
Server Hardware
Be sure to look at the diagram because the text description does not convey an important fact: when you can eliminate the unneeded duplications from multiple operating systems and duplicated code libraries, those reclaimed resources can be put to use for more applications, or used to reduce cloud costs.
Serverless computing takes that kind of virtualization one step further, by allowing you to scale the individual functions of your application to match users’ momentary needs. This is possible because:
- While a virtual machine takes minutes to boot up, a single application function can be activated in hundredths of a second.
- Similarly, while it takes a minute or so for a virtual machine to power down, a single function can be deactivated in hundredths of a second.
- Billing for compute resources can be done in hundredths-of-a-second increments, to very closely match the scaling capabilities of serverless computing.
Developers package up application functions, with just the code libraries that they need to run—which is a very different approach to software development than industries are used to. Additional software code is needed to manage the micro-scaling aspect, but the payoff comes in how quickly and affordably a cloud-based application can now scale up and down to meet very high levels of demand.
This article is not a tutorial about serverless computing—I didn’t even include a diagram for it.
The purpose for this article is to explain the purpose of serverless computing, so that you can understand why so much investment is going into cloud infrastructure and applications for serverless computing. This is the immediate future of cloud computing (which continues to evolve), and hopefully the very near future of highly scalable and affordable cloud-based security applications.
Ray Bernard, PSP CHS-III, is the principal consultant for Ray Bernard Consulting Services (RBCS), a firm that provides security consulting services for public and private facilities (www.go-rbcs.com). He is the author of the Elsevier book Security Technology Convergence Insights available on Amazon. Mr. Bernard is a Subject Matter Expert Faculty of the Security Executive Council (SEC) and an active member of the ASIS International member councils for Physical Security and IT Security.

